THORChain developers and security experts are working to neutralize a surge in fraudulent recovery schemes following a recent security incident that led to a reported loss of protocol funds. The decentralized liquidity network confirmed that malicious actors are targeting users with sophisticated “refund” portals and fake support accounts designed to drain assets from unsuspecting victims. This secondary wave of attacks follows an exploit where a substantial volume of digital assets was reportedly siphoned from the protocol’s cross-chain infrastructure.
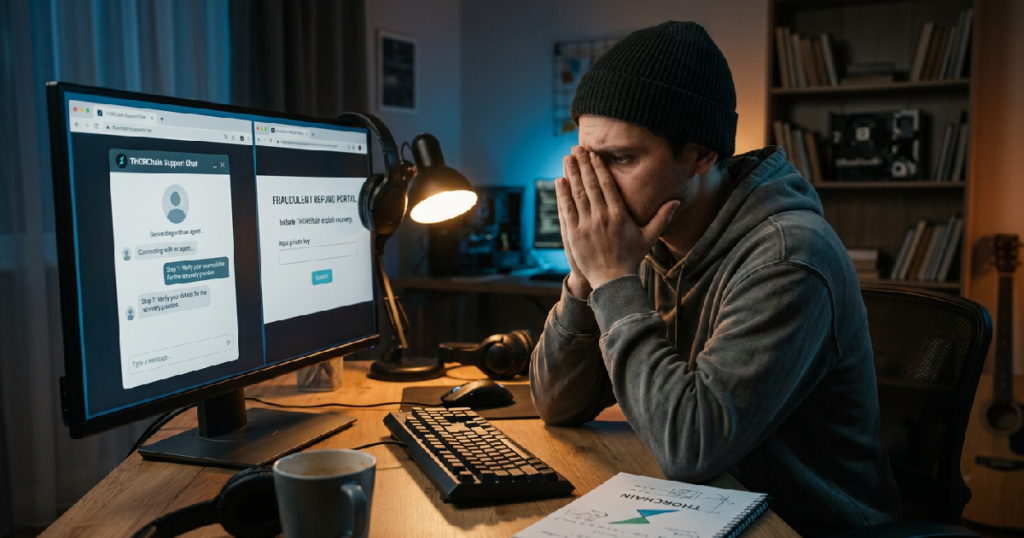
The original breach reportedly involved a vulnerability within the network’s bridging mechanism, which allowed an attacker to move assets out of the system. While engineering teams have reportedly addressed the technical loophole, the subsequent social engineering campaign has created a new set of challenges for the community. Fraudsters are reportedly impersonating official moderators on social media platforms to direct users toward malicious sites. These platforms often promise to reimburse lost tokens in exchange for “wallet verification” or private seed phrases.
Because the network operates on a decentralized basis, there is no central authority capable of reversing transactions once a user provides access to their wallet. As Bitcoin price analysis shows market resistance affects overall sentiment, the volatility often makes users more susceptible to these high-pressure tactics. Security teams emphasize that verified social media channels are the only reliable source of information regarding recovery efforts.
Forensics and Asset Tracking Initiatives
The protocol is reportedly collaborating with blockchain forensics specialists to map the movement of the stolen capital. Investigators are monitoring several high-value wallets associated with the breach, documenting how the funds are moving through various decentralized exchanges and mixing services. This tracking process is critical for alerting centralized platforms that might inadvertently process the assets, allowing them to freeze accounts if the perpetrator attempts to convert the holdings into fiat currency.
The investigation has renewed discussions regarding the inherent risks of cross-chain bridges. Recent market shifts, including increased activity in AI-driven DEXs, have highlighted how the complexity of smart contracts can create unforeseen attack vectors. For THORChain, the current priority is ensuring that the network architecture remains resilient against both direct exploits and the coordinated phishing campaigns that often follow them.
Recognizing Recovery Scams
Recovery scams are a persistent threat in the decentralized finance space because they prey on individuals who have already experienced financial loss. The network’s core contributors have issued reminders that the protocol will never request private keys or seed phrases to facilitate a return of funds. Many of these fraudulent sites utilize “drainer” scripts that are capable of emptying a wallet the moment a user signs a single transaction, leaving little room for error.
This rise in opportunistic fraud mirrors a period of broader uncertainty in the digital asset sector. As crypto liquidations rise alongside macro warning signs, scammers often find that anxiety-driven markets provide an ideal environment for their operations. Users are urged to remain skeptical of any direct messages or sponsored search results that promise immediate financial restitution.
Future Protocol Security and Automation
In response to the exploit, the community is debating potential upgrades to the protocol’s “emergency pause” functions. While the system was eventually halted to mitigate the impact of the breach, some contributors suggest that the response time must be further automated. Speeding up the interval at which validators can reach a consensus to suspend bridge activity would provide a more effective circuit breaker during active security events.
The situation remains fluid as the attacker reportedly moves funds in small increments to evade automated monitoring systems. The focus for the network remains on user safety and the prevention of further losses through social engineering. While the investigation continues, the protocol is expected to provide a detailed technical post-mortem to the community in the coming weeks. For now, participants are advised to utilize hardware wallets and adhere strictly to official documentation to mitigate the risk of further compromise.